Enterprise Information Security Architecture (EISA)
Enterprise Information Security Architecture (EISA) is the process of instituting a complete information security solution to the architecture of an enterprise, ensuring the security of business information at every point in the architecture. In other words, it is the enterprise and its activities that are to be secured, and the security of computers and networks is only a means to this end.[1]
EISA Framework[2]
EISA is not simply about building a wall between enterprise IT systems and the rest of the world. More importantly, it is a security architecture that aligns with the strategies and objectives of the enterprise, while also taking into consideration the importance of the free flow of information from all levels of the organization (internal to vendors to customers, etc.).
The development of this security architecture framework is purposely constructed to outline the current, intermediate, and target reference architectures, allowing them to align programs of change. This framework provides a rigorous taxonomy of the organization that clearly identifies what processes the business performs and detailed information about how those processes are executed and secured.
This framework goes into many levels of detail that vary according to practical considerations such as budget. This allows decision makers to make the most informed decisions about where to invest their resources and where to align organizational goals and processes to support core missions or business functions.
The Structure and Content of an EISA Framework
The primary function of EISA is to document and communicate the artifacts of the security program in a consistent manner. As such, the primary deliverable of EISA is a set of documents connecting business drivers with technical implementation guidance. These documents are developed iteratively through multiple levels of abstraction.
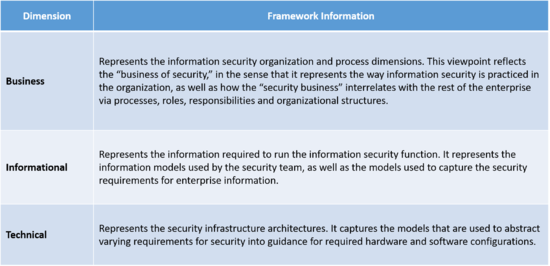
The three key dimensions of the EISA framework are as follows:
The EISA should describe how security is woven into the fabric of the business. The EISA process must allow inputs from and interface points with design components from other planning disciplines. Then, as the architecture and security processes mature, the EISA can have a more symbiotic relationship with the enterprise architecture, allowing further changes to be integrated easily.
Enterprise Information Security Architecture Topics[3]
- Positioning
Enterprise information security architecture was first formally positioned by Gartner in their whitepaper called “Incorporating Security into the Enterprise Architecture Process”. This was published on 24 January 2006. Since this publication, security architecture has moved from being a silo based architecture to an enterprise focused solution that incorporates business, information and technology. The picture below represents a one-dimensional view of enterprise architecture as a service-oriented architecture. It also reflects the new addition to the enterprise architecture family called “Security”. Business architecture, information architecture and technology architecture used to be called BIT for short. Now with security as part of the architecture family it has become BITS.
Security architectural change imperatives now include things like
Business roadmaps Legislative and legal requirements Technology roadmaps Industry trends Risk trends Visionaries Goals Provide structure, coherence and cohesiveness. Must enable business-to-security alignment. Defined top-down beginning with business strategy. Ensure that all models and implementations can be traced back to the business strategy, specific business requirements and key principles. Provide abstraction so that complicating factors, such as geography and technology religion, can be removed and reinstated at different levels of detail only when required. Establish a common "language" for information security within the organization Methodology The practice of enterprise information security architecture involves developing an architecture security framework to describe a series of "current", "intermediate" and "target" reference architectures and applying them to align programs of change. These frameworks detail the organizations, roles, entities and relationships that exist or should exist to perform a set of business processes. This framework will provide a rigorous taxonomy and ontology that clearly identifies what processes a business performs and detailed information about how those processes are executed and secured. The end product is a set of artifacts that describe in varying degrees of detail exactly what and how a business operates and what security controls are required. These artifacts are often graphical.
Given these descriptions, whose levels of detail will vary according to affordability and other practical considerations, decision makers are provided the means to make informed decisions about where to invest resources, where to realign organizational goals and processes, and what policies and procedures will support core missions or business functions.
A strong enterprise information security architecture process helps to answer basic questions like:
What is the information security risk posture of the organization? Is the current architecture supporting and adding value to the security of the organization? How might a security architecture be modified so that it adds more value to the organization? Based on what we know about what the organization wants to accomplish in the future, will the current security architecture support or hinder that? Implementing enterprise information security architecture generally starts with documenting the organization's strategy and other necessary details such as where and how it operates. The process then cascades down to documenting discrete core competencies, business processes, and how the organization interacts with itself and with external parties such as customers, suppliers, and government entities.
Having documented the organization's strategy and structure, the architecture process then flows down into the discrete information technology components such as:
Organization charts, activities, and process flows of how the IT Organization operates Organization cycles, periods and timing Suppliers of technology hardware, software, and services Applications and software inventories and diagrams Interfaces between applications - that is: events, messages and data flows Intranet, Extranet, Internet, eCommerce, EDI links with parties within and outside of the organization Data classifications, Databases and supporting data models Hardware, platforms, hosting: servers, network components and security devices and where they are kept Local and wide area networks, Internet connectivity diagrams Wherever possible, all of the above should be related explicitly to the organization's strategy, goals, and operations. The enterprise information security architecture will document the current state of the technical security components listed above, as well as an ideal-world desired future state (Reference Architecture) and finally a "Target" future state which is the result of engineering tradeoffs and compromises vs. the ideal. Essentially the result is a nested and interrelated set of models, usually managed and maintained with specialised software available on the market.
Such exhaustive mapping of IT dependencies has notable overlaps with both metadata in the general IT sense, and with the ITIL concept of the configuration management database. Maintaining the accuracy of such data can be a significant challenge.
Along with the models and diagrams goes a set of best practices aimed at securing adaptability, scalability, manageability etc. These systems engineering best practices are not unique to enterprise information security architecture but are essential to its success nonetheless. They involve such things as componentization, asynchronous communication between major components, standardization of key identifiers and so on.
Successful application of enterprise information security architecture requires appropriate positioning in the organization. The analogy of city-planning is often invoked in this connection, and is instructive.
An intermediate outcome of an architecture process is a comprehensive inventory of business security strategy, business security processes, organizational charts, technical security inventories, system and interface diagrams, and network topologies, and the explicit relationships between them. The inventories and diagrams are merely tools that support decision making. But this is not sufficient. It must be a living process.
The organization must design and implement a process that ensures continual movement from the current state to the future state. The future state will generally be a combination of one or more
Closing gaps that are present between the current organization strategy and the ability of the IT security dimensions to support it Closing gaps that are present between the desired future organization strategy and the ability of the security dimensions to support it Necessary upgrades and replacements that must be made to the IT security architecture based on supplier viability, age and performance of hardware and software, capacity issues, known or anticipated regulatory requirements, and other issues not driven explicitly by the organization's functional management. On a regular basis, the current state and future state are redefined to account for evolution of the architecture, changes in organizational strategy, and purely external factors such as changes in technology and customer/vendor/government requirements, and changes to both internal and external threat landscapes over time.
See Also
Enterprise Architecture
Enterprise Architecture Framework
Enterprise Architecture Management (EAM)
Enterprise Architecture Value Framework (EAVF)
Application Architecture
Business Architecture
Architected, Model-Driven Development (AMD)
Architected Rapid Application Development (ARAD)
Architectural Pattern
Architectural Principles
Risks in Architecture
Architectural Style
Architecture Description Language (ADL)
Architecture Development Method (ADM)
Architecture Driven Modernization
Architecture Tradeoff Analysis Method (ATAM)
IT Governance (Governance of Information Technology)
Corporate Governance
Governance
Governance, Risk And Compliance (GRC)
Information Architecture
Security Architecture
Information Security
Information Security Governance
Security Reference Model (SRM)
Cyber Security
References
- ↑ Defining Enterprise Information Security Architecture (EISA) Daniel K. Sigei
- ↑ EISA Framework RSI Security
- ↑ Enterprise Information Security Architecture Topics Wikipedia