Access Method
What is Access Method?[1]
An Access Method is a software component, operating system service, or network interface that handles the storage/retrieval and sending/receipt of data. Access methods provide an application programming interface (API) for programmers to perform these services, which rely on low-level, specialized instructions. In the 1960s, access methods were introduced by IBM as part of the mainframe OS/360 to provide access to data stored on disks, magnetic tapes, and other external storage devices. In non-mainframe operating systems, this function is handled by device drivers.
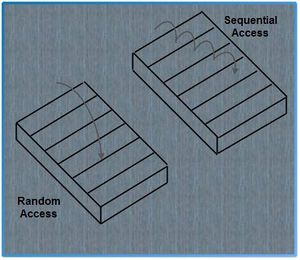
There are two types of access methods: random access and sequential access.[2]
The terms random access and sequential access are often used to describe data files. A random-access data file enables you to read or write information anywhere in the file. In a sequential-access file, you can only read and write information sequentially, starting from the beginning of the file. Both types of files have advantages and disadvantages. If you are always accessing information in the same order, a sequential-access file is faster. If you tend to access information randomly, random access is better.
To go from point A to point Z in a sequential-access system, you must pass through all intervening points. In a random-access system, you can jump directly to point Z.Disks are random access media, whereas tapes are sequential access media. (see figure below)
source: e Computer Notes
Commonly used access methods include the following:[3]
- QSAM (Queued Sequential Access Method) is a heavily used access method. QSAM arranges records sequentially in the order that they are entered to form sequential data sets and anticipates the need for records based on their order. The system organizes records with other records. To improve performance, QSAM reads these records into storage before they are requested, a technique known as queued access.
- BSAM (Basic Sequential Access Method) is used for special cases. BSAM arranges records sequentially in the order in which they are entered. Unlike QSAM, however, the user– rather than the system– organizes records with other records into blocks.
- BDAM (Basic Direct Access Method), which is becoming obsolete, arranges records in any sequence your program indicates and retrieves records by actual or relative address. If you do not know the exact location of a record, you can specify a point in the data set where a search for the record is to begin. Data sets organized this way are called direct data sets.
- BPAM (Basic Partitioned Access Method) arranges records as members of a partitioned data set (PDS) or a partitioned data set extended (PDSE) on DASD. You can use BPAM to view a UNIX directory and its files as if it were a PDS. (You can view each PDS, PDSE, or UNIX member sequentially with BSAM or QSAM.)
- VSAM (Virtual Sequential Access Method) is used for more complex applications. VSAM arranges records by an index key, relative record number, or relative byte addressing. VSAM is used for direct or sequential processing of fixed-length and variable-length records on DASD. Data that is organized by VSAM is cataloged for easy retrieval.
Access methods are identified primarily by the data set organization. z/OS® users, for example, use the basic sequential access method (BSAM) or queued sequential access method (QSAM) with sequential data sets. There are times when an access method identified with one organization can be used to process a data set organized in a different manner. For example, a sequential data set (not an extended-format data set) created using BSAM can be processed by the basic direct access method (BDAM), and vice versa. Another example is UNIX® files, which you can process using BSAM, QSAM, basic partitioned access method (BPAM), or virtual storage access method (VSAM).
Binding of Access Methods[4]
An access method may be specified at various times:
- When the operating system is designed. In this case, all files use the same method.
- When the file is created. Thus, every time the file is opened, the same access method will be used.
- When the file is opened. Several processes can have the same file open and access it differently.
Access Methods - Storage[5]
- Disk Access Methods: Indexed access methods are widely used to keep track of records in a file and files on a disk. The index is a table of contents with pointers to the location of each file on the disk or each record within the file. A common approach is the indexed sequential access method (ISAM), which uses an index in sequential order that points to records stored in random order. For the fastest retrieval, their direct access methods convert the record's identifying field, such as account number, into a physical storage address. The pure sequential method may also be used if direct access is not required.
- Communications Access Methods: Local area network (LAN) access methods, such as CSMA/CD in Ethernet, transfer data to and from connected computers on the network. These methods reference layers 1 and 2 of the OSI model. Mainframe access methods, such as IBM's TCAM and VTAM, transfer data between a host computer and remote terminals. These routines place the data into frames with appropriate control codes and reference layers 3, 4, and 5 of the OSI model.
- Tape Access Methods: Tapes use the sequential access method (SAM), which keeps records in order by a key field such as account number. Each record must be compared to find the desired one. Modern drives allow fast forwarding to index points where different groups of records are stored. This provides a direct access capability to sections of the tape, although very slow in comparison to disks.
Purpose of Access Methods[6]
System/360 and successor systems perform input/output using a special program for an I/O channel, a processor dedicated to controlling peripheral storage device access and data transfer to and from main memory. Channel programs are composed of channel command words (CCWs). Programming those is a complex task requiring detailed knowledge of the hardware characteristics. Channel programs are initiated by a START IO instruction issued by the operating system. This is usually front-ended by the Execute Channel Program (EXCP) macro for application programmer convenience. EXCP issues an SVC (supervisor call instruction) that directs the operating system to issue the START IO on the application's behalf.
Access methods provide:
- Ease of programming - programmer would no longer deal with specific device procedures, including error detection and recovery tactics in each and every program. A program designed to process a sequence of 80-character records would work no matter where the data are stored.
- Ease of hardware replacement - programmer would no longer alter a program when data should be migrated to a newer model of storage device, provided it supports the same access methods.
- Ease shared data set access - an access method is a trusted program, that allows multiple programs to access the same file while ensuring basic data integrity and system security.
Unlike systems derived from Unix, where all files and devices are considered to be an unformatted stream of bytes, mainframes offer a variety of data options and formats, such as varying types and sizes of records, and different ways of accessing data, such as via record keys. Access methods provide programs with a way of dealing with this complexity.
- Programs can read or write a record or block of data and wait until the input/output operation is complete (queued access methods) or allow the operation to be started and the program to continue to run, waiting for the completion at a later time (basic access methods).
- Programs can specify the size and number of buffers for a file. The same buffer or pool can be used for multiple files, allowing blocks of data to be read from one file and written to another without requiring data movement in memory.
- Programs can specify the type of error recovery to be used in case of input/output errors.
See Also
References
