Software-Defined WAN (SD-WAN)
A Software-Defined Wide Area Network (SD-WAN) is a virtual WAN architecture that allows enterprises to leverage any combination of transport services – including MPLS, LTE and broadband internet services – to securely connect users to applications. An SD-WAN uses a centralized control function to securely and intelligently direct traffic across the WAN. This increases application performance, resulting in enhanced user experience, increased business productivity and reduced costs for IT.[1]
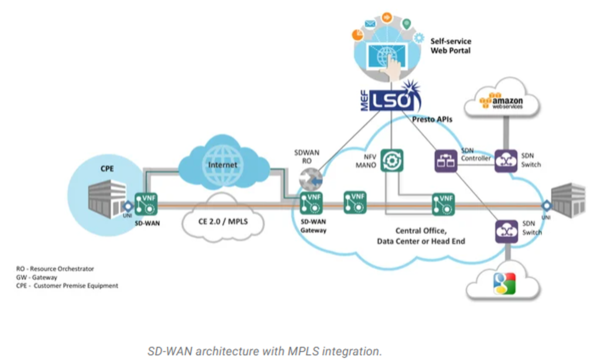
SD-WAN Architecture[2]
SD-WAN uses an abstracted architecture for its network. In an abstracted architecture, the network is divided into two parts: the control plane and the forwarding plane. This architecture moves the control plane to a centralized location like an organization’s headquarters. That way, the network can be managed remotely without the need for an on-premises IT crew.
There are three main components to an SD-WAN: The SD-WAN edge, the controller, and the orchestrator.
- The SD-WAN edge is where the network endpoints reside. This can be a branch office, a remote data center, or cloud platform.
- An SD-WAN Orchestrator is the virtualized manager for network, overseeing traffic and applying policy and protocol set by operators.
- The SD-WAN Controller centralizes management, and enables operators to see the network through a single pane of glass, and set policy for the orchestrator to execute.
These components make up the basic structure of an SD-WAN. In addition, there are three main types of SD-WAN architecture: on-premises, cloud-enabled, and cloud-enabled with a backbone.
- An On-premises SD-WAN is where the SD-WAN hardware resides on-site. Network operators can directly access and manage the network and the hardware it resides on, and it does not use the cloud for its connections. This makes making it ideal for sensitive information that cannot be sent over the internet.
- Cloud-enabled SD-WANs connect to a virtual cloud gateway over the internet, which makes the network more accessible, and provides better integration and performance with cloud-native applications.
- Cloud-Enabled with Backbone SD-WANs give organizations an extra backup by connecting the network with a nearby point of presence (PoP), such as within a data center. It allows an SD-WAN to switch from public internet to a private connection, which adds an extra layer of security and consistency in case the connection is overwhelmed or fails.
History[3]
WANs were very important for the development of networking technologies in general and were for a long time the most important application of networks both for military and enterprise applications. The ability to communicate data over large distances was one of the main driving factors for the development of data communications technologies, as it made it possible to overcome the distance limitations, as well as shortening the time necessary to exchange messages with other parties.
Legacy WANs technologies allowed communication over circuits connecting two or more endpoints. Earlier technologies supported point-to-point communication over a slow speed circuit, usually between two fixed locations. As technology evolved, WAN circuits became faster and more flexible. Innovations like circuit and packet switching (in the form of X.25, ATM and later Internet Protocol or Multiprotocol Label Switching communications) allowed communication to become more dynamic, supporting ever-growing networks.
The need for strict control, security and quality of service meant that multinational corporations were very conservative in leasing and operating their WANs. National regulations restricted the companies that could provide local service in each country, and complex arrangements were necessary to establish truly global networks. All that changed with the growth of the Internet, which allowed entities around the world to connect to each other. However, over the first years, the uncontrolled nature of the Internet was not considered adequate or safe for private corporate use.
Independent of safety concerns, connectivity to the Internet became a mandatory necessity to the point where every branch required Internet access. At first, due to the safety concerns, private communication were still done via WAN, and communication with other entities (including customers and partners) moved to the Internet.
As the Internet grew in reach and maturity, companies started to evaluate how to leverage it for private corporate communications. During the early 2000s, application delivery over the WAN became an important topic of research and commercial innovation. Over the next decade, the increasing computing power made it possible to create software-based appliances that were able to analyze traffic and make informed decisions in real time, making it possible to create large-scale overlay networks over the public Internet that could replicate all the functionality of legacy WANs, at a fraction of the cost.
SD-WAN combines several technologies to create full-fledged private networks, with the ability to dynamically share network bandwidth across the connection points. Additional enhancements include central controllers, zero-touch provisioning, integrated analytics and on-demand circuit provisioning, with some network intelligence based in the cloud, allowing centralized policy management and security.
Networking publications started using the term SD-WAN to describe this new networking trend as early as 2014.
How Does SD-WAN Work?[4]
There are several characteristics that are generally attributed to SD-WANs. Let’s walk through them and learn more about the way SD-WAN works.
- Centralized control: The primary means of control in an SD-WAN is centralized. It often resides in a SaaS application running on a public cloud. Control is decoupled from the hardware to simplify network management and improve the delivery of services. SD-WAN appliances (and virtual appliances) follow operational rules passed down from the central controller. This greatly reduces or eliminates the need to manage gateways and routers on an individual basis.
- Multi-connection, multi-transport: SD-WAN gateways support hybrid WAN, which implies that each gateway can have multiple connections using different transports—MPLS, broadband Internet, LTE, etc. A virtual private network (VPN) is typically set up across each WAN connection for security. Consequently, the SD-WAN can be an overlay spanning a diverse communications infrastructure.
- Dynamic path selection: Another feature of SD-WAN is dynamic path selection—the ability to automatically and selectively route traffic onto one WAN link or another depending on network conditions or traffic characteristics. Packets may be steered onto a particular link because another link is down or not working very well, or to balance network traffic across all available links. SD-WAN can also identify packets by application, user, source/destination, etc. and send them down one path or another based on those characteristics.
- Policy-based management: Policy is what determines where dynamic path selection will steer traffic and what level of priority (quality of service, or QoS) it is given. Business intentions can be implemented as policies via the central management console. New and updated policies are translated into operational rules and downloaded to all SD-WAN gateways and routers under control. A policy may be created, for example, to ensure the best performance for VoIP and interactive web conferences by giving their packets transmission priority and routing them onto low-latency paths. Cost savings can be realized by sending file back-ups across a broadband Internet connection. WAN traffic that requires a high level of security can be restricted to private connections (e.g., MPLS) between sites and required to pass through a robust security stack when entering the enterprise.
- Service chaining: An additional characteristic of SD-WAN is the ability chain it together with other network services. WAN optimization (acceleration) is often combined with SD-WAN to improve network and application performance. Internet traffic leaving and entering a branch office may be routed across a VPN to a cloud-base security service to strike a balance between performance, security, and cost.
See Also
References
- ↑ Definition - What Does Software-Defined WAN (SD-WAN) Mean? Silver Peak
- ↑ SD-WAN Architecture SDX Central
- ↑ History of SD-WAN Wikipedia
- ↑ How Does SD-WAN Work? Riverbed