Business Model for Information Security (BMIS)
What is the Business Model for Information Security (BMIS)?
The Business Model for Information Security began life as a model for systemic security management, created by Dr. Laree Kiely and Terry Benzel at the USC Marshall School of Business Institute for Critical Information Infrastructure Protection. In 2008 ISACA acquired from the university the right to develop the model to help embed its concepts in information security practices globally. The model takes a business-oriented approach to managing information security. Its holistic and dynamic approach to information security within the context of business demonstrates to the enterprise that information security can be both predictive and proactive. The model can be used regardless of the size of the enterprise or the information security framework (if any) the enterprise currently has in place. The model is independent of any particular technology or technological changes over time. Likewise, it is applicable across industries, geographies, and regulatory and legal systems. It includes not only traditional information security but also privacy, linkages to risk, physical security, and compliance.[1]
A critical piece of the model that differentiates it from many others is the importance it places on organizational culture. Creating an intentional security culture is a primary objective for the model, as applied to information security. The intentional information security culture focuses on the enterprise’s governance needs. This type of culture has several important characteristics:
- Alignment of information security and business objectives
- A risk-based approach
- Balance among the organization, people, process and technology
- Allowance for the convergence of security strategies
BMIS can be viewed as a three dimensional Model best visualized as a pyramid (see Figure below). All aspects of the Model interact with each other. If any one part of the Model is changed, not addressed, or managed inappropriately, it will distort the balance of the Model.[2]
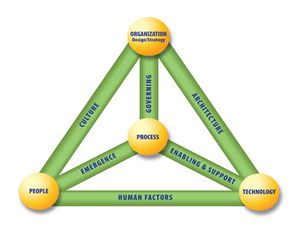
source: ISACA
The Elements of Business Model for Information Security (BMIS)[3]
The four elements of the model are:
- 1. Organization Design and Strategy -An organization is a network of people, assets and processes interacting with each other in defined roles and working toward a common goal. An enterprise’s
strategy specifies its business goals and the objectives to be achieved as well as the values and missions to be pursued. It is the enterprise’s formula for success and sets its basic direction. The strategy should adapt to external and internal factors. Resources are the primary material to design the strategy and can be of different types (people, equipment, know-how). Design defines how the organization implements its strategy. Processes, culture and architecture are important to determining the design.
- 2. People -The people element represents the human resources and the security issues that surround them. It defines who implements (through design) each part of the strategy. It represents a human collective and must take into account values, behaviors and biases. Internally, it is critical for the information security manager to work with the human resources and legal departments to address issues such as:
- Recruitment strategies (access, background checks, interviews, roles and responsibilities)
- Employment issues (location of office, access to tools and data, training and awareness, movement within the enterprise)
- Termination (reasons for leaving, timing of exit, roles and responsibilities, access to systems, access to other employees)
Externally, customers, suppliers, media, stakeholders and others can have a strong influence on the enterprise and need to be considered within the security posture.
- 3. Process - Process includes formal and informal mechanisms (large and small, simple and complex) to get things done and provides a vital link to all of the dynamic interconnections. Processes identify, measure, manage and control risk, availability, integrity and confidentiality, and they also ensure accountability. They derive from the strategy and implement the operational part of the organization element. To be advantageous to the enterprise, processes must:
- Meet business requirements and align with policy
- Consider emergence and be adaptable to changing requirements
- Be well documented and communicated to appropriate human resources
- Be reviewed periodically, once they are in place, to ensure efficiency and effectiveness
- 4. Technology -The technology element is composed of all of the tools, applications and infrastructure that make processes more efficient. As an evolving element that experiences frequent changes, it has its own dynamic risks. Given the typical enterprise’s dependence on technology, technology constitutes a core part of the enterprise’s infrastructure and a critical component in accomplishing its mission. Technology is often seen by the enterprise’s management team as a way to resolve security threats and risks. While technical controls are helpful in mitigating some types of risks, technology should not be viewed as an information security solution. Technology is greatly impacted by users and by organizational culture. Some individuals still mistrust technology, some have not learned to use it and others feel it slows them down. Regardless of the reason, information security managers must be aware that many people will try to sidestep technical controls.
Dynamic Interconnections of BMIS[4]
The dynamic interconnections are what link the elements together and exert a multidirectional force that pushes and pulls as things change. Actions and behaviors that occur in the dynamic interconnections can force the model out of balance or bring it back to equilibrium. The six dynamic interconnections are:
1. Governing—Governing is the steering of the enterprise and demands strategic leadership. Governing sets limits within which an enterprise operates and is implemented within processes to monitor performance, describe activities and achieve compliance while also providing adaptability to emergent conditions. Governing incorporates ensuring that objectives are determined and defined, ascertaining that risks are managed appropriately, and verifying that the enterprise’s resources are used responsibly.
2. Culture—Culture is a pattern of behaviors, beliefs, assumptions, attitudes and ways of doing things. It is emergent and learned, and it creates a sense of comfort.5 Culture evolves as a type of shared history as a group goes through a set of common experiences. Those similar experiences cause certain responses, which become a set of expected and shared behaviors. These behaviors become unwritten rules, which become norms that are shared by all people who have that common history. It is important to understand the culture of the enterprise because it profoundly influences what information is considered, how it is interpreted and what will be done with it. Culture may exist on many levels, such as national (legislation/regulation, political and traditional), organizational (policies, hierarchical style and expectations) and social (family, etiquette). It is created from both external and internal factors, and is influenced by and influences organizational patterns.
3. Enabling and support—The enabling and support dynamic interconnection connects the technology element to the process element. One way to help ensure that people comply with technical security measures, policies and procedures is to make processes usable and easy. Transparency can help generate acceptance for security controls by assuring users that security will not inhibit their ability to work effectively. Many of the actions that affect both technology and processes occur in the enabling and support dynamic interconnection. Policies, standards and guidelines must be designed to support the needs of the business by reducing or eliminating conflicts of interest, remaining flexible to support changing business objectives, and being acceptable and easy for people to follow.
4. Emergence—Emergence—which connotes surfacing, developing, growing and evolving—refers to patterns that arise in the life of the enterprise that appear to have no obvious cause and whose outcomes seem impossible to predict and control. The emergence dynamic interconnection (between people and processes) is a place to introduce possible solutions such as Feedback loops; alignment with process improvement; and consideration of emergent issues in system design life cycle, change control, and risk management.
5. Human factors—The human factors dynamic interconnection represents the interaction and gap between technology and people and, as such, is critical to an information security program. If people do not understand how to use the technology, do not embrace the technology or will not follow pertinent policies, serious security problems can evolve. Internal threats such as data leakage, data theft and misuse of data can occur within this dynamic interconnection. Human factors may arise because of age, experience level and/or cultural experiences. Because human factors are critical components in maintaining balance within the model, it is important to train all of the enterprise’s human resources on pertinent skills.
6. Architecture—A security architecture is a comprehensive and formal encapsulation of the people, processes, policies and technology that comprise an enterprise’s security practices. A robust business information architecture is essential to understanding the need for security and designing the security architecture. It is within the architecture dynamic interconnection that the enterprise can ensure defense in depth. The design describes how the security controls are positioned and how they relate to the overall IT architecture. An enterprise security architecture facilitates
security capabilities across lines of businesses in a consistent and a cost-effective manner and enables enterprises to be proactive with their security investment decisions.
See Also
IT Governance
ITIL
Val IT
Risk IT
COSO
CMMI
IT Assurance Framework (ITAF)
IT Governance Framework
ICT Investment Framework
Control Objectives for Information and Related Technology (COBIT)
Business Model
Information Security
Information Security Governance
Information Technology Security Assessment
References
- ↑ What is Business Mode] for Information Security (BMIS)? isaca.org
- ↑ BMIS - A Three Dimensional Model ics.forth.gr
- ↑ What are the Elements of Business Model for Information Security (BMIS)? Yulia Cherdantseva, COMSC, Cardiff University
- ↑ The Dynamic Interconnections of BMIS ISACA
Further Reading
- How to Manage Cloud Risks Based on the BMIS Model Youjin Song and Yasheng Pang
- Information Security from a Business Perspective BusinessComputingWorld
