Network Protocol
What is Network Protocol?
A network protocol is an established set of rules that determine how data is transmitted between different devices in the same network. Essentially, it allows connected devices to communicate with each other, regardless of any differences in their internal processes, structure, or design. Network protocols are the reason you can easily communicate with people all over the world, and thus play a critical role in modern digital communications. Similar to the way that speaking the same language simplifies communication between two people, network protocols make it possible for devices to interact with each other because of predetermined rules built into devices’ software and hardware. Neither local area networks (LAN) nor wide area networks (WAN) could function the way they do today without the use of network protocols.[1]
Standardized network protocols are important for providing a common language so that the network devices can successfully send and receive information. Rules of network protocol include guidelines that regulate the following characteristics of a network: access method, allowed physical topologies, types of cabling, and speed of data transfer. One of the most popular models that are used to build open communication between two network systems is the Open Systems Interconnection (OSI) model.[2]
Network protocols incorporate all the processes, requirements, and constraints of initiating and accomplishing communication between computers, servers, routers, and other network-enabled devices. They must be confirmed and installed by the sender and receiver to ensure network/data communication and apply to software and hardware nodes that communicate on a network. Network protocols are developed and published by several groups according to certain industry standards. The most important ones include:
- World Wide Web Consortium (W3C)
- International Telecommunication Union (ITU)
- International Organization for Standardization (ISO)
- Internet Engineering Task Force (IETF)
- The Institute of Electrical and Electronics Engineers (IEEE)
A protocol suite is a set of different network protocols that cooperate to exchange information and enable internet connectivity across various layers. For example, the TCP/IP suite comprehends the Transmission Control Protocol (TCP), User Datagram Protocol (UDP), Internet Protocol (IP), and Hypertext Transfer Protocol (HTTP) or File Transfer Protocol (FTP). Each one of them allows the transmission of data between devices at the information packet level (mainly TCP, and UDP as well to add an additional layer of stability), Internet address level (IP), and display level (HTTP and FTP).[3]
In exploring the various network protocols that enable seamless communication across the internet, it's crucial to understand the foundational role of Client Server Architecture. This model underpins the operation of these protocols, facilitating efficient data exchange between clients and servers.
The Typical Structure of a Network Protocol[4]
The structure described in any one of the protocol data packets includes important information about the data exchange package, such as:
- The sender and receiver
- The type of the packet (e.g. connect, disconnect, or pure data)
- The packet length
- A checksum
This information is provided as a header to the payload data or attached as a preview. Moreover, in some protocols; fixed packet sequences for the connection establishment and release are described. These actions cause further traffic on the data lines – the so-called overhead. This overhead is undesirable because it burdens the capacity, but due to the more important tasks, making the logs, usually it is used. With User Datagram Protocol (UDP), in the transport layer, a minimal overhead is available that does not ensure end-to-end control of the transmission. In contrast, in the Transmission Control Protocol (TCP), the checksum for the test is to verify the data packet is complete. If the checksum does not meet the expectations of the test algorithm, the data packet is discarded and requested again at the sending site.
How Network Protocols Are Implemented[5]
Modern operating systems contain built-in software services that implement support for some network protocols. Applications like web browsers contain software libraries that support the high-level protocols necessary for that application to function. For some lower-level TCP/IP and routing protocols, support is implemented in direct hardware (silicon chipsets) for improved performance.
Each packet transmitted and received over a network contains binary data (ones and zeros that encode the contents of each message). Most protocols add a small header at the beginning of each packet to store information about the message's sender and its intended destination. Some protocols also add a footer at the end. Each network protocol can to identify messages of its own kind and process the headers and footers as part of moving data among devices.
A group of network protocols that work together at higher and lower levels is often called a protocol family. Students of networking traditionally learn about the OSI model that conceptually organizes network protocol families into specific layers for teaching purposes.
Types of Network Protocols[6]
There are three main types of network protocols. These include network communication protocols, network management protocols, and network security protocols:
- Network Communication Protocols: Communication protocols are vital to the functioning of a network. In fact, computer networks can't exist without these protocols. These protocols formally describe the formats and rules by which data is transferred over the network. This is a must-have for exchanging messages between your computing systems and in telecommunications, applying to both hardware and software. Communication protocols also handle authentication and error detection as well as the syntax, synchronization, and semantics that both analog and digital communications must abide by to function.
- HTTP – One of the most familiar protocols, hypertext transfer protocol (HTTP) is often referred to as the protocol of the internet. HTTP is an application layer protocol that allows the browser and server to communicate.
- TCP – Transmission Control Protocol (TCP) separates data into packets that can be shared over a network. These packets can then be sent by devices like switches and routers to the designated targets.
- UDP – User Datagram Protocol (UDP) works in a similar way to TCP, sending packets of data over the network. The key difference between the two is that TCP ensures a connection is made between the application and server, but UDP does not.
- IRC – Internet Relay Chat (IRC) is a text-based communication protocol. Software clients are used to communicating with servers and sending messages to other clients. This protocol works well on networks with a large number of distributed machines.
- Network Management Protocols: Network management protocols help define the policies and procedures used to monitor, manage and maintain your computer network, and help communicate these needs across the network to ensure stable communication and optimal performance across the board. Generally, network managers can use a management protocol to troubleshoot connections between host and client devices. Management protocols provide network managers with the host connection's status, availability, packet or data loss, and other related information about the health of the network connection. The policies managed by management protocols can be applied to all devices on the network, including computers, switches, routers, and even servers. Two of the most common types of network management protocols include Simple Network Management Protocol (SNMP) and Internet Control Message Protocol (ICMP).
- SNMP – Simple Network Management Protocol (SNMP) is used to monitor and manage network devices. This TCP-based protocol allows administrators to view and modify endpoint information to alter the behavior of devices across the network. SNMP relies on the use of agents to collect and send data to an overarching SMNP manager, which in turn queries agents and gets their responses.
- ICMP – Internet Control Message Protocol (ICMP) is primarily used for diagnostic purposes. Managed devices on the network can use this protocol to send error messages, providing information regarding network connectivity issues between devices.
- Network Security Protocols: Network security protocols work to ensure that data in transit over the network's connections stays safe and secure. These protocols also define how the network secures data from any attempts to review or extract said data by illegitimate means. This helps ensure that no unauthorized users, services, or devices access your network data, and this works across all data types and network mediums being used. Usually, network security protocols rely on encryption and cryptography to secure data so that only special algorithms, formulas, and logical keys can make this data accessible. Some of the most popular protocols for network security include Secure Socket Layer (SSL), Secure File Transfer Protocol (SFTP), and Secure Hypertext Transfer Protocol (HTTPS).
- SSL – A Secure Socket Layer (SSL) is a network security protocol primarily used for ensuring secure internet connections and protecting sensitive data. This protocol can allow for server/client communication as well as server/server communication. Data transferred with SSL is encrypted to prevent it from being readable.
- SFTP – Secure File Transfer Protocol (SFTP), as its name might suggest, is used to securely transfer files across a network. Data is encrypted and the client and server are authenticated.
- HTTPS – Secure Hypertext Transfer Protocol is the secure version of HTTP. Data sent between the browser and server are encrypted to ensure protection.
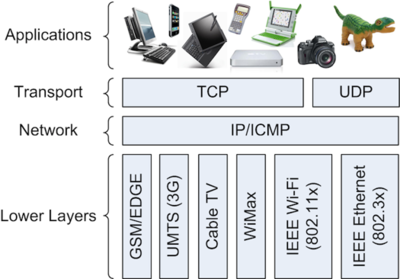
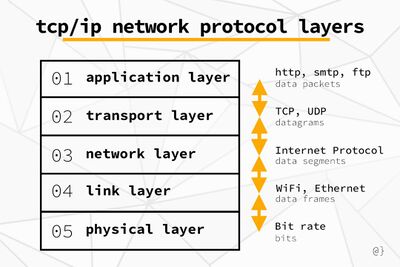
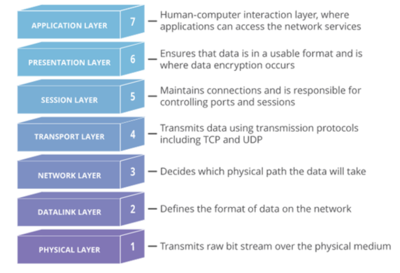
Network Protocol Layers[7]
Network protocol layering is a system of service hierarchy used in networked computer communication. Each layer offers a set of guaranteed services to the layer above such that higher-level abstractions can be built while making assumptions about lower-level transport services. These services allow for ensuring a certain level of operability such that higher-layered protocols can take the lower-level features for granted. Another benefit is that developers of layer-specific applications can focus on their primary goals rather than wrestling with the functionality of other layers. For example, in TCP/IP communication, the transport layer offers a Reliable Data Protocol (RDP) service. This allows developers to focus on the logic of networked applications rather than the delivery of generated data. For example, web browsers can use HTTP protocol—an application layer protocol—to ensure communication between clients and hosts is facilitated without data loss. In other words; the developers of Mozilla Firefox only have to focus on what data is sent from users to websites and not how that data is sent.
The two most popular network layer models as the OSI Stack and TCP/IP Stack. These two models are very similar but have some differences that are worth noting.
- TCP/IP Protocol Stack
- Application
- Transport
- Network
- Link
- Physical
- OSI Protocol Stack
- Application
- Presentation
- Session
- Transport
- Network
- Link
- Physical
Each network layer is responsible for maintaining a collection of protocols. These protocols make certain guarantees such that upper layers can focus on more abstract pursuits. For example, the application layer uses HTTP protocol, which uses the transport layers TCP protocol, which uses the network layer’s IP protocol all to ensure a website loads when you type the address into your web browser. This layered system helps from having to reinvent the wheel for higher-level applications. Network protocol layering is a powerful abstraction by which developers and engineers can harness existing technology. Rather than re-implementing previous solutions, application developers can assume predictable functions based on previously-defined industry standards. This results in application developers focusing on user interactivity, ISPs focusing on service quality, and hardware manufacturers focusing on new and improved features.
Protocols that Run on the Network Layer[8]
- IPsec: Internet Protocol Security (IPsec) sets up encrypted, authenticated IP connections over a virtual private network (VPN). Technically IPsec is not a protocol, but rather a collection of protocols that includes the Encapsulating Security Protocol (ESP), Authentication Header (AH), and Security Associations (SA).
- ICMP: The Internet Control Message Protocol (ICMP) reports errors and provides status updates. For example, if a router is unable to deliver a packet, it will send an ICMP message back to the packet's source.
- IGMP: The Internet Group Management Protocol (IGMP) sets up one-to-many network connections. IGMP helps set up multicasting, meaning multiple computers can receive data packets directed at one IP address.
See Also
- TCP/IP (Transmission Control Protocol/Internet Protocol)
- Telnet
- Protocol Stack
- Internet Protocol (IP)
- File Transfer Protocol (FTP)
- POP (Post Office Protocol)
- VoIP (Voice Over Internet Protocol)
- Extensible Authentication Protocol (EAP)
- Hypertext Transfer Protocol (HTTP)
- User Datagram Protocol (UDP)
- Protocol Data Unit (PDU)
- Network Control Program (NCP)
- Transmission Control Protocol (TCP)
- Time Triggered Protocol (TTP)
- Business Transaction Protocol (BTP)
- Common Alerting Protocol (CAP)
- SMTP (Simple Mail Transfer Protocol)
- Advanced Message Queuing Protocol (AMQP)
- Simple Object Access Protocol (SOAP)
- Internet Message Access Protocol (IMAP)
- IP Network
- Ethernet Industrial Protocol (Ethernet/IP)
- Simple Network Management Protocol (SNMP)
- Access Media Gateways (AMG)
- Secure Sockets Layer (SSL)
- Internet Message Access Protocol (IMAP)
- Synchronous Optical Network (SONET)