Network Security
Definition of Network Security[1]
Network Security is an organization’s strategy that enables guaranteeing the security of its assets including all network traffic. It includes both software and hardware technologies. Access to the network is managed by effective network security, which targets a wide range of threats and then arrests them from spreading or entering in the network. Network security is an integration of multiple layers of defenses in the network and at the network. Each network security layer implements policies and controls. Access to networks is gained by authorized users, whereas, malicious actors are indeed blocked from executing threats and exploits.
Network security is a subgroup of networking. It involves securing the connected network infrastructure from the core to the edge of the network perimeter. Typically managed by a network administrator, network security involves implementing IT security policy and deploying network software and hardware to:
- Protect the network, its infrastructure and all its traffic from external cyberattacks
- Protect all IT assets and resources available via the network from unauthorized access
- Ensure authorized users have adequate access to these network IT assets and resources to perform work effectively [2]
Safeguarding data during transmission is paramount in network security. A solid understanding of Client Server Architecture informs the implementation of encryption, firewalls, and secure protocols, ensuring the integrity and confidentiality of client-server communications.
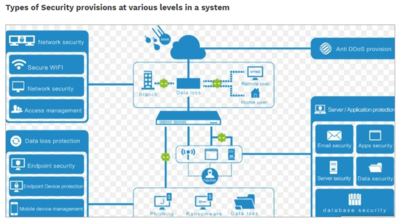
Types of Network Security[3]
- Firewalls: Firewalls put up a barrier between your trusted internal network and untrusted outside networks, such as the Internet. They use a set of defined rules to allow or block traffic. A firewall can be hardware, software, or both.
- Email security: Email gateways are the number one threat vector for a security breach. Attackers use personal information and social engineering tactics to build sophisticated phishing campaigns to deceive recipients and send them to sites serving up malware. An email security application blocks incoming attacks and controls outbound messages to prevent the loss of sensitive data.
- Antivirus Software and anti-malware software: "Malware," short for "malicious software," includes viruses, worms, Trojans, ransomware, and spyware. Sometimes malware will infect a network but lie dormant for days or even weeks. The best antimalware programs not only scan for malware upon entry, but also continuously track files afterward to find anomalies, remove malware, and fix damage.
- Network segmentation: Software-defined segmentation puts network traffic into different classifications and makes enforcing security policies easier. Ideally, the classifications are based on endpoint identity, not mere IP addresses. You can assign access rights based on role, location, and more so that the right level of access is given to the right people and suspicious devices are contained and remediated.
- Access Control: Not every user should have access to your network. To keep out potential attackers, you need to recognize each user and each device. Then you can enforce your security policies. You can block noncompliant endpoint devices or give them only limited access. This process is network access control (NAC).
- Application security: Any software you use to run your business needs to be protected, whether your IT staff builds it or whether you buy it. Unfortunately, any application may contain holes, or vulnerabilities, that attackers can use to infiltrate your network. Application security encompasses the hardware, software, and processes you use to close those holes.
- Behavioral analytics: To detect abnormal network behavior, you must know what normal behavior looks like. Behavioral analytics tools automatically discern activities that deviate from the norm. Your security team can then better identify indicators of compromise that pose a potential problem and quickly remediate threats.
- Data Loss Prevention (DLP): Organizations must make sure that their staff does not send sensitive information outside the network. Data loss prevention, or DLP, technologies can stop people from uploading, forwarding, or even printing critical information in an unsafe manner.
- Intrusion Prevention System (IPS)s: An intrusion prevention system (IPS) scans network traffic to actively block attacks.
- Mobile device security: Cybercriminals are increasingly targeting mobile devices and apps. Within the next 3 years, 90 percent of IT organizations may support corporate applications on personal mobile devices. Of course, you need to control which devices can access your network. You will also need to configure their connections to keep network traffic private.
- Security information and event management: SIEM products pull together the information that your security staff needs to identify and respond to threats. These products come in various forms, including physical and virtual appliances and server software.
- Virtual Private Network (VPN): A virtual private network encrypts the connection from an endpoint to a network, often over the Internet. Typically, a remote-access VPN uses IPsec or Secure Sockets Layer to authenticate the communication between device and network.
- Web security: A web security solution will control your staff’s web use, block web-based threats, and deny access to malicious websites. It will protect your web gateway on site or in the cloud. "Web security" also refers to the steps you take to protect your own website.
- Wireless security: Wireless networks are not as secure as wired ones. Without stringent security measures, installing a wireless LAN can be like putting Ethernet ports everywhere, including the parking lot. To prevent an exploit from taking hold, you need products specifically designed to protect a wireless network.
source: Software Testing Help
Evolution of Network Security[4]
“Things get worse slowly. People adjust” – David D. Clark, the Internet pioneer who is now working as a Senior Research Scientist at MIT’s Computer Science and Artificial Intelligence Laboratory (referring to the flaw in the network security design of the early Internet)
The need for network security dates back to the late 80s after a flaw in the network design slowly incrementalized its process. It started with the very design of the Internet, open and distributed. It was the time when no one felt the need to control communication among its users and mutual mistrust was out of the picture.
David D. Clark realized that humans tend to ignore existing problems, which often transforms into something even more disastrous. The Morris worm of 1988 wasn’t an intentional threat to the network security of that time. A worm is a standalone malware program capable of replicating itself to expand its reach to other computers while remaining active on the infected system. Well, the developer of the worm, Robert Morris intended to determine the size of the internet by propagating a self-written program across the networks, later infiltrating the Unix terminals with a known bug, and at the end, would duplicate itself through three attack vectors: sendmail, fingerd, and rsh/rexec. Little to his knowledge, the last instruction turned out to be a mistake. The Morris worm replicated itself drastically, damaging thousands of machines and vaporizing millions of dollars into thin air.
In the aftermath of the incident, Morris was charged with the first felony of the United States 1986 Computer Fraud and Abuse Act. He was not only sentenced to three years of probation but was fined with $10,050 and 400 hours of community service. Later, DARPA funded CERT/CC at Carnegie Mellon University, which improved the security of numerous software and the Internet. The Morris worm is now considered to be a legend for starting a wave of cyberattacks.
In short, what started with a small online community for a few researchers is now accessible to around 3.2 billion people around the globe. And with that, potential security related threats have also increased dramatically. After all these years, the cyber world is still facing the same challenge with much greater intensity. In fact, the situation is worsening with each passing year.
Network Security Concept[5]
Network security starts with authentication, commonly with a username and a password. Since this requires just one detail authenticating the user name—i.e., the password—this is sometimes termed one-factor authentication. With two-factor authentication, something the user 'has' is also used (e.g., a security token or 'dongle', an ATM card, or a mobile phone); and with three-factor authentication, something the user 'is' is also used (e.g., a fingerprint or retinal scan).
Once authenticated, a firewall enforces access policies such as what services are allowed to be accessed by the network users. Though effective to prevent unauthorized access, this component may fail to check potentially harmful content such as computer worms or Trojans being transmitted over the network. Anti-virus software or an intrusion prevention system (IPS) help detect and inhibit the action of such malware. An anomaly-based intrusion detection system may also monitor the network like wireshark traffic and may be logged for audit purposes and for later high-level analysis. Newer systems combining unsupervised machine learning with full network traffic analysis can detect active network attackers from malicious insiders or targeted external attackers that have compromised a user machine or account.
Communication between two hosts using a network may be encrypted to maintain privacy.
Honeypots, essentially decoy network-accessible resources, may be deployed in a network as surveillance and early-warning tools, as the honeypots are not normally accessed for legitimate purposes. Techniques used by the attackers that attempt to compromise these decoy resources are studied during and after an attack to keep an eye on new exploitation techniques. Such analysis may be used to further tighten security of the actual network being protected by the honeypot. A honeypot can also direct an attacker's attention away from legitimate servers. A honeypot encourages attackers to spend their time and energy on the decoy server while distracting their attention from the data on the real server. Similar to a honeypot, a honeynet is a network set up with intentional vulnerabilities. Its purpose is also to invite attacks so that the attacker's methods can be studied and that information can be used to increase network security. A honeynet typically contains one or more honeypots.
How Network Security Works[6]
There are many layers to consider when addressing network security across an organization. Attacks can happen at any layer in the network security layers model, so your network security hardware, software and policies must be designed to address each area. Network security typically consists of three different controls: physical, technical and administrative. Here is a brief description of the different types of network security and how each control works.
- Physical Network Security: Physical security controls are designed to prevent unauthorized personnel from gaining physical access to network components such as routers, cabling cupboards and so on. Controlled access, such as locks, biometric authentication and other devices, is essential in any organization.
- Technical Network Security: Technical security controls protect data that is stored on the network or which is in transit across, into or out of the network. Protection is twofold; it needs to protect data and systems from unauthorized personnel, and it also needs to protect against malicious activities from employees.
- Administrative Network Security: Administrative security controls consist of security policies and processes that control user behavior, including how users are authenticated, their level of access and also how IT staff members implement changes to the infrastructure.
Principles of Network Security[7]
There are three principles within the concept of network security—confidentiality, integrity, and availability—which together are sometimes referred to as the “CIA triad.” A network can only be considered secure when it has all three elements in play simultaneously.
Confidentiality works to keep sensitive data protected and sequestered away from where it can be accessed by the average user. This goes hand-in-hand with the principle of availability, which seeks to ensure that data and resources are kept accessible for those who are authorized to access them. Challenges to availability can include DDoS attacks or equipment failure. The principle of integrity seeks to protect information from intentional or accidental changes in order to keep the data reliable, accurate, and trustworthy.
Every decision made regarding network security should be working to further at least one of these principles. This means that MSPs need to ask if each decision will ensure that data is kept confidential, that its integrity will be protected, and that it will be made more easily available to those with authorization to access it.
Network Security and the Cloud[8]
More and more enterprises are offloading some of their computing needs to cloud service providers, creating hybrid infrastructures where their own internal network has to interoperate seamlessly — and securely — with servers hosted by third parties. Sometimes this infrastructure itself is a self-contained network, which can be either physical (several cloud servers working together) or virtual (multiple VM instances running together and "networking" with each other on a single physical server).
To handle the security aspects, many cloud vendors establish centralized security control policies on their own platform. However, the trick here is that those security systems won't always match up with your policies and procedures for your internal networks, and this mismatch can add to the workload for network security pros. There are a variety of tools and techniques available to you that can help ease some of this worry, but the truth is that this area is still in flux and the convenience of the cloud can mean network security headaches for you.
Benefits of Network Security[9]
Network security exists to help your organization protect not only its sensitive information, but also its overall performance, reputation and even its ability to stay in business. Continued operational ability and an intact reputation are two key benefits of effective network security.
Companies that fall prey to cyberattacks often find themselves crippled from the inside out, unable to deliver services or effectively address customer needs. Similarly, networks play a major role in internal company processes, and when they come under attack, those processes may grind to a halt, further hampering an organization’s ability to conduct business or even resume standard operations. But perhaps even more damaging is the detrimental effect that a network breach can have on your business’s reputation.
Given the rising tide of identity theft and other dangers related to the theft of personal information, many customers are already hesitant when it comes to sharing data with businesses. And if a cyberattack should occur, many of these customers are likely to withdraw in favor of more secure alternatives. After all, why take the risk?
The loss or corruption of valuable data, along with a significant disruption to customer services and internal process, topped off with reputational injury that may persist long after other damages have been repaired — it’s not hard to see what’s at stake when it comes to network security. In fact, it’s been suggested that 66 percent of SMBs would have to shut down (either temporarily or permanently) after experiencing a data breach. And even larger, more established businesses may be unable to reclaim their former standing.
On the other hand, reliable network security software and hardware, coupled with the right policies and strategies, can help ensure that when cyberattacks occur, their impact will be minimal.
See Also
Network security is a critical aspect of information technology that involves implementing measures and protocols to protect the integrity, confidentiality, and accessibility of computer networks and data. It encompasses a range of practices designed to safeguard the network and data from unauthorized access, misuse, malfunction, modification, destruction, or improper disclosure.
- Firewall: A network security device that monitors and filters incoming and outgoing network traffic based on an organization's previously established security policies. At its most basic, a firewall is a barrier between a private internal network and the public internet.
- Intrusion Detection System (IDS) and Intrusion Prevention System (IPS): IDS is a monitoring system that detects suspicious activities and potential threats within a network. On the other hand, IPS not only detects but also prevents such threats by blocking detected malicious activities.
- Virtual Private Network (VPN): A technology that creates a safe and encrypted connection over a less secure network like the internet. VPNs extend a private network across a public network, allowing users to send and receive data as if their computing devices were directly connected to the private network.
- Antivirus and Anti-malware Software: Programs designed to detect, prevent, and remove malicious software, such as viruses, worms, trojans, ransomware, and spyware, that can compromise the security of a network and the devices connected to it.
- Encryption is the process of converting data or information into a code to prevent unauthorized access. It is a fundamental component of network security, ensuring that data transmitted across a network or stored on devices is secure.
- Secure Sockets Layer (SSL)/Transport Layer Security (TLS): Protocols that provide communications security over a computer network. Websites use SSL/TLS to secure all communications between their servers and web browsers.
- Phishing: A type of social engineering attack often used to steal user data, including login credentials and credit card numbers. It occurs when an attacker, masquerading as a trusted entity, dupes a victim into opening an email, instant message, or text message.
- (DoS) and Distributed Denial-of-Service (DDoS) Attacks: DoS is an attack meant to shut down a machine or network, making it inaccessible to its intended users. DDoS is a type of DoS attack where the perpetrator uses multiple compromised computer systems as sources of attack traffic.
- Multi-Factor Authentication (MFA): A security system that requires more than one method of authentication from independent categories of credentials to verify the user's identity for a login or other transaction. MFA combines two or more independent credentials: what the user knows (password), what the user has (security token), and what the user is (biometric verification).
- Security Information Event Management (SIEM): A set of tools and services offering a holistic view of an organization's information security. SIEM tools provide real-time visibility across an organization's information security systems by aggregating data from multiple sources and identifying deviations from the norm to detect attacks.
Network security is an evolving field that adapts to new threats and technologies. Implementing robust network security measures is essential for protecting an organization's information assets against the ever-growing landscape of cyber threats.
References
- ↑ What Does Network Security Mean? Comodo
- ↑ What is Network Security Palo Alto Networks
- ↑ Types of Network Security Cisco
- ↑ Evolution of Internet Security EC-Council
- ↑ Network Security Concept Wikipedia
- ↑ How does network security work? Forcepoint
- ↑ What are the principles of network security? Solarwind smsp
- ↑ Network Security and the Cloud CSO Online
- ↑ Benefits of Network Security Gigamon
