Access Control
Access Control is a fundamental component of data security that dictates who’s allowed to access and use company information and resources. Through authentication and authorization, access control policies make sure users are who they say they are and that they have appropriate access to company data. Access control can also be applied to limit physical access to campuses, buildings, rooms, and data centers.[1]
Access control is a broad term that describes policies and methods that ensure only verified individuals can physically or virtually touch items that they have permission to access. This process involves restricting access or granting permissions that allow someone to do something to a protected item. This includes having permissions to do any of the following to protected items (digital or physical resources):
- Access,
- Read,
- Modify,
- Communicate,
- Delete or otherwise destroy.
For longtime IT cybersecurity expert Greg Scott, access controls typically boil down to understanding the relationship between two specific terms: subjects and objects.
“Subjects are usually people or groups. Objects are usually files or directories. The key is, subjects access objects, and so access controls regulate how subjects access objects.”
In this understanding, objects could be resources that you want to protect from unauthorized access, use, or disclosure. And the subject is the user (or group of users or even non-person entities such as applications or services) that the access controls apply to. So, access controls (in a more technical sense) are the tools, policies, models, and mechanisms that enable you to grant or restrict access to your organization’s digital or physical resources. This includes everything from restricting or granting access to specific files and databases to IT systems and physical locations.
If you look at the definitions of access control on the National Institute of Standards and Technology (NIST) website, you’ll see a lot of variations. However, they all basically mean the same thing in a roundabout way: access control is a way for you to ensure that only the individuals (or groups) you choose have access to your sensitive data, applications, technologies, and critical infrastructure.
Basically, these types of physical and logical restrictions prevent unauthorized individuals from doing things they shouldn’t with your sensitive systems or data. Furthermore, they also help to prevent inadvertent exposure or disclosure of sensitive items.[2]
Types of access control[3]
Organizations must determine the appropriate access control model to adopt based on the type and sensitivity of data they’re processing. Older access models include discretionary access control (DAC) and mandatory access control (MAC), role based access control (RBAC) is the most common model today, and the most recent model is known as attribute based access control (ABAC).
- Discretionary access control (DAC): With DAC models, the data owner decides on access. DAC is a means of assigning access rights based on rules that users specify.
- Mandatory access control (MAC): MAC was developed using a nondiscretionary model, in which people are granted access based on an information clearance. MAC is a policy in which access rights are assigned based on regulations from a central authority.
- Role Based Access Control (RBAC): RBAC grants access based on a user’s role and implements key security principles, such as “least privilege” and “separation of privilege.” Thus, someone attempting to access information can only access data that’s deemed necessary for their role.
- Attribute Based Access Control (ABAC): In ABAC, each resource and user are assigned a series of attributes. “In this dynamic method, a comparative assessment of the user’s attributes, including time of day, position and location, are used to make a decision on access to a resource.”
It’s imperative for organizations to decide which model is most appropriate for them based on data sensitivity and operational requirements for data access. In particular, organizations that process personally identifiable information (PII) or other sensitive information types, including Health Insurance Portability and Accountability Act (HIPAA) or Controlled Unclassified Information (CUI) data, must make access control a core capability in their security architecture.
Access Control System Topologies[4]
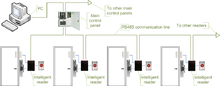
- Serial controllers. Controllers are connected to a host PC via a serial RS-485 communication line (or via 20mA current loop in some older systems). External RS-232/485 converters or internal RS-485 cards have to be installed, as standard PCs do not have RS-485 communication ports.
- Advantages:
- RS-485 standard allows long cable runs, up to 4000 feet (1200 m)
- Relatively short response time. The maximum number of devices on an RS-485 line is limited to 32, which means that the host can frequently request status updates from each device, and display events almost in real time.
- High reliability and security as the communication line is not shared with any other systems.
- Disadvantages:
- RS-485 does not allow Star-type wiring unless splitters are used
- RS-485 is not well suited for transferring large amounts of data (i.e. configuration and users). The highest possible throughput is 115.2 kbit/sec, but in most system it is downgraded to 56.2 kbit/sec, or less, to increase reliability.
- RS-485 does not allow the host PC to communicate with several controllers connected to the same port simultaneously. Therefore, in large systems, transfers of configuration, and users to controllers may take a very long time, interfering with normal operations.
- Controllers cannot initiate communication in case of an alarm. The host PC acts as a master on the RS-485 communication line, and controllers have to wait until they are polled.
- Special serial switches are required, in order to build a redundant host PC setup.
- Separate RS-485 lines have to be installed, instead of using an already existing network infrastructure.
- Cable that meets RS-485 standards is significantly more expensive than regular Category 5 UTP network cable.
- Operation of the system is highly dependent on the host PC. In the case that the host PC fails, events from controllers are not retrieved, and functions that require interaction between controllers (i.e. anti-passback) stop working.
- Advantages:

Access control system using serial controllers
- Serial main and sub-controllers. All door hardware is connected to sub-controllers (a.k.a. door controllers or door interfaces). Sub-controllers usually do not make access decisions, and instead forward all requests to the main controllers. Main controllers usually support from 16 to 32 sub-controllers.
- Advantages:
- Work load on the host PC is significantly reduced, because it only needs to communicate with a few main controllers.
- The overall cost of the system is lower, as sub-controllers are usually simple and inexpensive devices.
- All other advantages listed in the first paragraph apply.
- Disadvantages:
- Operation of the system is highly dependent on main controllers. In case one of the main controllers fails, events from its sub-controllers are not retrieved, and functions that require interaction between sub-controllers (i.e. anti-passback) stop working.
- Some models of sub-controllers (usually lower cost) do not have the memory or processing power to make access decisions independently. If the main controller fails, sub-controllers change to degraded mode in which doors are either completely locked or unlocked, and no events are recorded.
- Such sub-controllers should be avoided, or used only in areas that do not require high security.
- Main controllers tend to be expensive, therefore such a topology is not very well suited for systems with multiple remote locations that have only a few doors.
- All other RS-485-related disadvantages listed in the first paragraph apply.
- Advantages:

Access control system using serial main and sub-controllers
- Serial main controllers & intelligent readers. All door hardware is connected directly to intelligent or semi-intelligent readers. Readers usually do not make access decisions, and forward all requests to the main controller. Only if the connection to the main controller is unavailable, will the readers use their internal database to make access decisions and record events. Semi-intelligent reader that have no database and cannot function without the main controller should be used only in areas that do not require high security. Main controllers usually support from 16 to 64 readers. All advantages and disadvantages are the same as the ones listed in the second paragraph.
Access control system using serial main controller and intelligent readers
- Serial controllers with terminal servers. In spite of the rapid development and increasing use of computer networks, access control manufacturers remained conservative, and did not rush to introduce network-enabled products. When pressed for solutions with network connectivity, many chose the option requiring less efforts: addition of a terminal server, a device that converts serial data for transmission via LAN or WAN.
- Advantages:
- Allows utilizing the existing network infrastructure for connecting separate segments of the system.
- Provides a convenient solution in cases when the installation of an RS-485 line would be difficult or impossible.
- Disadvantages:
- Increases complexity of the system.
- Creates additional work for installers: usually terminal servers have to be configured independently, and not through the interface of the access control software.
- Serial communication link between the controller and the terminal server acts as a bottleneck: even though the data between the host PC and the terminal server travels at the 10/100/1000Mbit/sec network speed, it must slow down to the serial speed of 112.5 kbit/sec or less. There are also additional delays introduced in the process of conversion between serial and network data.
- All the RS-485-related advantages and disadvantages also apply.
- Advantages:
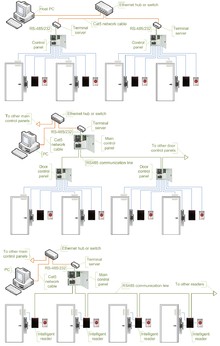
Access control systems using serial controllers and terminal servers
- Network-enabled main controllers. The topology is nearly the same as described in the second and third paragraphs. The same advantages and disadvantages apply, but the on-board network interface offers a couple of valuable improvements. Transmission of configuration and user data to the main controllers is faster, and may be done in parallel. This makes the system more responsive, and does not interrupt normal operations. No special hardware is required in order to achieve redundant host PC setup: in the case that the primary host PC fails, the secondary host PC may start polling network controllers. The disadvantages introduced by terminal servers (listed in the fourth paragraph) are also eliminated.

Access control system using network-enabled main controllers
- IP controllers. Controllers are connected to a host PC via Ethernet LAN or WAN.
- Advantages:
- An existing network infrastructure is fully utilized, and there is no need to install new communication lines.
- There are no limitations regarding the number of controllers (as the 32 per line in cases of RS-485).
- Special RS-485 installation, termination, grounding and troubleshooting knowledge is not required.
- Communication with the controllers may be done at the full network speed, which is important if transferring a lot of data (databases with thousands of users, possibly including biometric records).
- In case of an alarm, controllers may initiate connection to the host PC. This ability is important in large systems, because it serves to reduce network traffic caused by unnecessary polling.
- Simplifies installation of systems consisting of multiple sites that are separated by large distances. A basic Internet link is sufficient to establish connections to the remote locations.
- Wide selection of standard network equipment is available to provide connectivity in various situations (fiber, wireless, VPN, dual path, PoE)
- Disadvantages:
- The system becomes susceptible to network related problems, such as delays in case of heavy traffic and network equipment failures.
- Access controllers and workstations may become accessible to hackers if the network of the organization is not well protected. This threat may be eliminated by physically separating the access control network from the network of the organization. Most IP controllers utilize either Linux platform or proprietary operating systems, which makes them more difficult to hack. Industry standard data encryption is also used.
- Maximum distance from a hub or a switch to the controller (if using a copper cable) is 100 meters (330 ft).
- Operation of the system is dependent on the host PC. In case the host PC fails, events from controllers are not retrieved and functions that require interaction between controllers (i.e. anti-passback) stop working. Some controllers, however, have a peer-to-peer communication option in order to reduce dependency on the host PC.
- Advantages:

Access control system using IP controllers
- IP readers. Readers are connected to a host PC via Ethernet LAN or WAN.
- Advantages:
- Most IP readers are PoE capable. This feature makes it very easy to provide battery backed power to the entire system, including the locks and various types of detectors (if used).
- IP readers eliminate the need for controller enclosures.
- There is no wasted capacity when using IP readers (e.g. a 4-door controller would have 25% of unused capacity if it was controlling only 3 doors).
- IP reader systems scale easily: there is no need to install new main or sub-controllers.
- Failure of one IP reader does not affect any other readers in the system.
- Disadvantages:
- In order to be used in high-security areas, IP readers require special input/output modules to eliminate the possibility of intrusion by accessing lock and/or exit button wiring. Not all IP reader manufacturers have such modules available.
- Being more sophisticated than basic readers, IP readers are also more expensive and sensitive, therefore they should not be installed outdoors in areas with harsh weather conditions, or high probability of vandalism, unless specifically designed for exterior installation. A few manufacturers make such models.
- The advantages and disadvantages of IP controllers apply to the IP readers as well.
- Advantages:
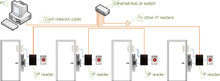
Access control system using IP readers
Components of Access Control[5]
At a high level, access control is about restricting access to a resource. Any access control system, whether physical or logical, has five main components:
- Authentication: The act of proving an assertion, such as the identity of a person or computer user. It might involve validating personal identity documents, verifying the authenticity of a website with a digital certificate, or checking login credentials against stored details.
- Authorization: The function of specifying access rights or privileges to resources. For example, human resources staff are normally authorized to access employee records and this policy is usually formalized as access control rules in a computer system.
- Access: Once authenticated and authorized, the person or computer can access the resource.
- Manage: Managing an access control system includes adding and removing authentication and authorization of users or systems. Some systems will sync with G Suite or Azure Active Directory, streamlining the management process.
- Audit: Frequently used as part of access control to enforce the principle of least privilege. Over time, users can end up with access they no longer need, e.g. when they change roles. Regular audits minimize this risk.
See Also
- Security
- Security Architecture
- Secure Sockets Layer (SSL)
- Securities and Exchange Commission (SEC)
- Security Event Management (SEM)
- Security Information Management (SIM)
- Security Management
- Security Policy
- Security Reference Model (SRM)
- Information Security
- Information Security Governance
- Information Security Management System (ISMS)
- Information Security Risk Management (ISRM)
- Access Control Facility (ACF2)
- Access Control List (ACL)
- Access Method
- Access Network
- Access Point (AP)
