Applications Portfolio Analysis (APA)
Applications Portfolio Analysis (APA) is a tool to divide current and proposed applications into three categories — utility, enhancement and frontier — based on the degree to which they contribute to the enterprise’s performance. The utility category is essential but does not enhance the enterprise’s performance (e.g., payroll); the enhancement category contains applications that improve the enterprise’s performance based on the use of established technology (e.g., documentation automation); and the frontier category is aimed at greatly improving enterprise performance (e.g., through aggressive use of rule-based decision support) but usually entails substantial risk. The management issues for each category are, respectively, cost, opportunity identification and innovation. The planning process should consider the best balance among the three categories to gain optimal future performance and the appropriate value from the application of IT.[1]
The Dimensions of Applications Portfolio Analysis (APA)[2]
Top down analysis of enterprise applications can be done by evaluating application’s business value and technical condition and determining whether the application should be evolved/maintained, modernized, retired/consolidated or re-positioned. In addition, onw must also manage the IT asset life cycle and align IT spending with business needs. (See figure below on how to interpret results)
- 1. Business Value: Measures of the application’s value to the business
- Business Criticality – The extent to which the loss of this application would affect the organisation's capability to conduct core business processes
- Competitive Advantage – The extent to which the application enables a capability that results in greater revenue, lower cost or differentiate the organisation in the marketplace
- Current Effectiveness – The level to which the application effectively supports the business operations
- Breadth of Usage – The extent of which the application is being used. Is it being used locally by a small group of users?
- 2. Application Risk: View of the vulnerabilities of the application across multiple risk categories
- Regulatory Compliance – Federal and state regulations, privacy legislation
- Data Sensitivity – Sensitivity level of managed data ranges from low (public info), to medium (info available to most staff), to high (private/proprietary info)
- Security – Security policy compliance, threat levels, auditing requirements Urgency of action – Urgency of corrective action required to improve the business value or effectiveness
- Capacity Constraints – Capacity constraints (e.g. CPU, memory, network) preventing expansion of use
- Vendor Viability – Software vendor, support, End-of-Life, vendors of required underlying products
- IT Skills – Continued availability of knowledgeable IT staff - Historical Failure Rate – Track record of failure
- 3. Operational Costs: Annual costs to support the application
- Application Development Staff Cost
- Licensing Cost
- Infrastructure Cost
- 4. Technical Condition: Assessment of the technical condition and system quality of the application
- Accessibility: Is the application available where you require it?
- Scalability: How will it respond if the number of users or business volume double?
- Availability: Is it available when you require it?
- Data Accuracy: Is data consistent and standard?
- Performance: Does it respond in time? Does it complete processing in time?
- Recoverability: After an unplanned outage, is it up and functioning in time?
- Usability: Relative to the complexity of the task, is it intuitive to use without extensive training?
- Extendibility: Can it easily provide new or extended functionality without changes to many (unrelated) parts of the application?
- System Isolation: How much are other systems isolated from changes in this application?
- Reusability: How easy is it to reuse existing functions or components to support new requirements, and to expose services or components to be reused by other applications?
- Product Alignment: What is the level of alignment with product standards?
- Architecture Alignment: What is the level of alignment with enterprise architecture?
- Alignment Roadblock: What is the impact of roadblocks in preventing the future alignment with product standards and architecture?
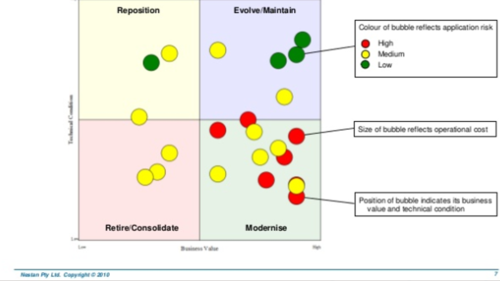
source: Nestan Pty Ltd
Applications Portfolio Analysis (APA) Process - The Time Method [3]
Big, complex applications are often a fairly small percentage of the total application count., support a lot of business value, and merit a detailed analysis. How does one economically categorize and overhaul the thousands of smaller applications that form the rest of the portfolio? One way would be to create a routine process that will rapidly align the thousands of applications into tolerate, invest, migrate and eliminate (TIME) categories — ideally driving extensive application elimination. Begin the process by assessing key factors of each application in order to categorize each application. Ideally the scope is the entire application inventory but it may be segmented based on current strategic business initiatives with a process, risk, cost, or value perspective. There are various methods to categorize the applications. A popular format is based on the 2X2, 4 quadrant matrix. An example is the “TIME” (Tolerate, Invest, Migrate, Eliminate) method as defined by Gartner. (see figure below)
- T – Tolerate applications that provide good enough business value but may have an old architecture or not be well integrated. Without APM, this is probably the largest category.
- I – Invest in strategic or newer applications in order to increase value and use.
- M – Migrate technologies that have high business value but have issues the with people, data, or technologies that support it. The technology may be unsupported or people may be on the verge of retiring with a declining pool of replacement skills.
- E – Eliminate applications that no longer provide sufficient business value.
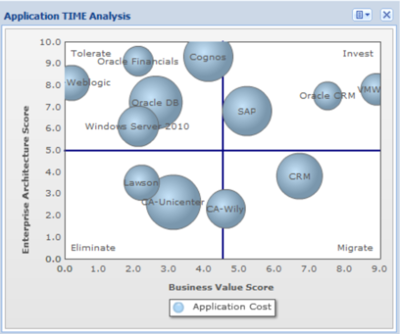
source: Eric Weinstein
See Also
- Application Performance Management (APM)
- Application Portfolio Management (APM)
- Project Portfolio Management (PPM)
- Project Portfolio Rationalization
References
- ↑ What is Application Portfolio Analysis? Gartner
- ↑ The 4 Dimensions of Applications Portfolio Analysis (APA) Ann Tse
- ↑ The Time Method in the Applications Portfolio Analysis (APA) Process Eric Weinstein
Further Reading
- Reducing Technology Risk in M&As – The Case For Application Portfolio Analysis Cast Highlight
- Application Portfolio Analysis for OffShoring Raghuvir Kamath, PMP®
- Application Portfolio Analysis: How to save millions from BAU budgets Catalyst.co.uk
