Network Mapping
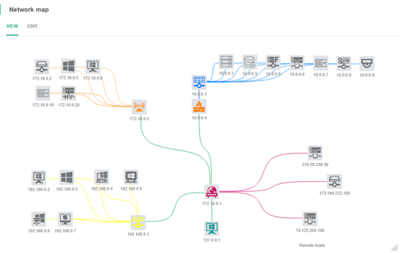
Network Mapping is a process used to discover and visualize physical and virtual network connectivity via a group of interrelated tasks that facilitate the creation of a network map, including flow charts, network diagrams, topology detection and device inventories. It is geared toward the creation of visual aids and materials that can be used for a broad array of purposes, especially network maintenance. Network mapping systems use an active probing method to gather network data by sending probe packets that hop from node to node, which return information to the mapping system with the IP address and other technical details. In large networks like the Internet and its smaller constituents, this probe may be limited to gathering publicly available, non-confidential and general node information. Network mapping allows network administrators (NA) to visualize and break down complex networks into smaller portions, allowing the NA to analyze and view the network, check for connection errors and pull up details that facilitate an issue's root cause analysis. By using a mapping system's active monitoring module, administrators can track network changes in real time. This is useful for network providers and Internet service providers (ISP), as well as anyone that operates a large, complex network[1]
Network mapping software is closely integrated with the system and directly interacts with a network tree. It allows for advanced, thorough management, and even control, of the network infrastructure as a whole and particularly of the interactive connected devices. Due to this fact, it is not merely a visualizing scheme tool, but a full-blown interactive tool for managing devices. Furthermore, with most Network Mapping software users are not restricted to managing only real, physical devices through the network mapping tool; standard and custom virtual objects can also be managed.
Mapping Network Environments[2]
- Mapping the Physical: Mapping the actual runs of cable, their terminations, etc., may be tantalizing in its concrete-ness. It is, in fact, the closest visual representation of your “true” network environment. But there is a question of depth. Do you need every NIC, whether it has something plugged in or not? How about pin-outs? How about cable types? Cable manufacturers? Backup power lines? And so on. And of course, it’s nearly impossible to generate this type of map automatically.
- Mapping the Logical: Most network maps fall into this category. It is less interested in the physical layer than the way data connections behave in the environment, and therefore more accurately represents the movement of data even if you can’t always tell how the cabling works.
- Mapping the Functional: This type of map is the one your users and systems administrators want to see: a map representing the way application traffic logically (but not physically) flows through an environment. That said, as a network map, it’s sub-optimal because application servers aren’t always physical. The depth of the map is in question, and it’s purposely obfuscating the network infrastructure in favor of showing data flows, so its usefulness to network engineers is minimal.
How Does Network Mapping Work?[3]
Network mapping is the process of visualizing all the devices on your network, how they’re connected, and how the overall network is structured. The network map generally equips you with information about whether the network is functioning properly or whether any particular device has a problem.
Networks are set up in different structures, also called topologies. The structure can have a major effect on how your network functions, what happens when a device or server goes down, and how complex it is to manage. When you map your network, you’re basically mapping its topology into a visual network diagram. Here are the main network topologies to be aware of:
- Bus – A bus network is set up in a straight line, allowing data to flow through the network from the server to each node one by one
- Ring – In a ring, network the nodes are arranged in a circle, and data can flow around the circle in one or both directions
- Tree: In a tree topology, a server has multiple branches of nodes coming off it. This is a bit more robust than a bus or ring topology, as with a tree topology, if one of the branches has a problem with a node, the rest of the network will still function. With ring and bus topologies, a problem with one node can cause the whole network to go down
- Star – A star topology has one central node with all others coming off it in a star pattern
- Mesh – A mesh network has connections between all the nodes and servers, like a lattice or mesh. It has high failover protection because if one node goes down, the network can reroute the data to get it where it needs to go
- Hybrid – A hybrid topology is simply a combination of any or all the above network structures and is very common as networks get larger
Enterprise Network Mapping<ref>Enterprise Network Mapping Wikipedia</ref>
Many organizations create network maps of their network system. These maps can be made manually using simple tools such as Microsoft Visio, or the mapping process can be simplified by using tools that integrate auto network discovery with Network mapping, one such example being the IP Fabric platform. Many of the vendors from the Notable network mappers list enable you to customize the maps and include your own labels, add un-discoverable items and background images. Sophisticated mapping is used to help visualize the network and understand relationships between end devices and the transport layers that provide service. Items such as bottlenecks and root cause analysis can be easier to spot using these tools.
There are three main techniques used for network mapping: SNMP based approaches, active probing and route analytics.
The SNMP based approach retrieves data from Router and Switch MIBs in order to build the network map. The active probing approach relies on a series of traceroute-like probe packets in order to build the network map. The route analytics approach relies on information from the routing protocols to build the network map. Each of the three approaches have advantages and disadvantages in the methods that they use.
References
- ↑ Definition - What Does Network Mapping Mean? Techopedia
- ↑ Mapping Network Environments Solarwinds
- ↑ How Does Network Mapping Work? DNS Stuff