Shadow IT
Definition - What is Shadow IT[1]
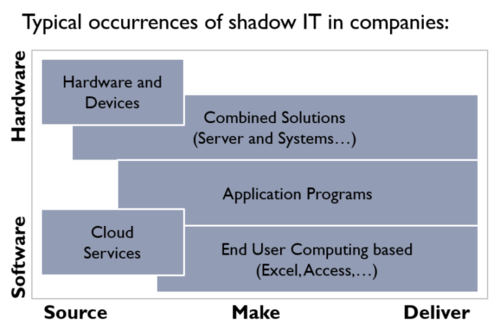
Shadow IT is a term often used to describe information-technology systems and solutions built and used inside organizations without explicit organizational approval. It is also used, along with the term "Stealth IT", to describe solutions specified and deployed by departments other than the IT department. Shadow IT is considered by many an important source for innovation and such systems may turn out to be prototypes for future approved IT solutions. On the other hand, shadow IT solutions are not often in line with the organization's requirements for control, documentation, security, reliability, etc., although these issues can apply equally to authorized IT solutions.
The consequence of stealth IT is that it opens up both security and legal risks for the company. Unfortunately, IT doesn’t discover many of the stealth IT incidences until they have caused significant damage. By then it is a much bigger problem to fix. The IT department loses control on activities and services in the organization and often Sys Admins find themselves solving issues that they originally had nothing to do with.
While the IT department may not handle the physical infrastructure or management of Shadow IT applications and services, IT does carry the burden of ensuring security and compliance for the corporate data that employees create and transmit through Shadow IT sources. This creates mixed feelings toward Shadow IT, as some enterprises are willing to embrace the innovation and increased productivity it can deliver, while others aren't as willing to look past the increased risk of security and compliance complications of Shadow IT.[2]
Shadow IT Technologies[3]
Here are some common stealth or shadow IT technologies that may already exist in your company.
- Online/Cloud Storage: With the numerous online or cloud-based storage services like Dropbox, SkyDrive, and Google Drive, users have quick and easy methods to store files online. They can sync them between computers, access data from anywhere, and even easily install and use on personal devices.
- Free File Transfer: Company email accounts generally have limits on file attachment sizes. Users frequently need to exceed these limits, and end up finding a work-around by using external file transfer sites that offer a free service. Online services like YouSendIt or DropBox let you upload large files to their servers; you can then send a link to anyone you want so it can be downloaded.
- Personal Email Accounts: Companies require their employees to conduct business using the corporate email system. However, users frequently use their personal email—Hotmail or Gmail accounts either because they want to attach large files, connect using their personal devices, or because they think the company email is too slow.
- Cloud-based IP Telephony services: Employees often use cloud-based IP Telephony services like Skype or Google Voice to communicate with others both inside and outside the organization. The problem here is that the company stands to lose data or valuable customer information once the employee leaves the organization.
- Website Hosting: When an employee goes completely outside IT to put up a project or department Website with a 3rd-party hosting provider, there comes a point where that employee leaves the organization. As a result, there is nobody to maintain the site, the subscription expires and the site goes down.
- Infrastructure/Hardware Purchase: Companies employ hardware standards to help make support manageable throughout the organization. But problems can occur is an executive makes his own hardware purchase and expects IT to support it. For example, application development departments use Amazon Web Services (AWS) to have their production environments ready to go in less time than their own IT processes.
source: BITCO3
Establishing Policies Around Shadow IT[4]
A critical first step for dealing with Shadow IT is to clearly map an organization’s global IT landscape per the impact that each family/group or individual resources will potentially have on corporate core business. The CIO needs to list and classify the known market available Shadow IT resources in three categories: Sanctioned; Authorized (not Sanctioned yet irrelevant); Prohibited (not sanctioned and dangerous). This is a corporate matter that does not merely concern a technical perspective and therefore should be dealt with by the CIO. This is something that impacts people and their motivation as well as potentially some business-critical processes or information, so the policy should typically be defined and sponsored at the board level. Some key items need to be leveraged like:
- Since by law some information on a collaborator’s workstation (like emails) may be that collaborator’s property, should the workstation environment also be classified by the company as such?
- Is a collaborator entitled to use any tools that he/she may find suitable to boost his/her productivity if they pose no risk for the corporation? If so what is the registry/ \approval process that needs to be followed?
- What shall be the impact and compliance probability from the collaborators towards prohibitions? Meaning it is pointless to have someone spending hours trying to find a way to break a prohibition in place instead of doing their work.
Managing Shadow IT[5]
While the effects of Rogue IT can be challenging for organizations, it is also true that through good management you can use this phenomenon to turn it into a business advantage. Let’s see some recommendations to successfully manage Shadow IT:
- Locate the Shadow IT: According to a survey by the Frost and Sullivan Institute, sponsored by McAfee; 80% of employees agree that they have incurred in this practice. This means that there is a high probability that this trend may be taking place in your organization. Therefore, the best thing to do is to carry out an in-depth analysis that allows you to filter the exchange of information with external elements. From there, it will be easier for you to identify processes involving unauthorized solutions.
- Find the reason why: There are several reasons why an employee may be motivated to practice Shadow IT, such as the fact that this phenomenon allows users in the organization to use the latest applications without waiting for IT to verify or approve them. Carry out an evaluation to determine the main reasons for the appearance of the Invisible IT. As a result, you will be able to obtain valuable information that will enable CIOs to take more effective measures to meet the user’s needs, related to the use of effective tools.
- Minimize the risks: Instead of banning the use of Shadow IT applications, seek to implement security solutions to control their use. Invest in a tool that allows you to protect your systems in a comprehensive way, by protecting the organization’s sensitive data both in the internal flow and in interactions in the cloud. Such solutions should give you full visibility into your assets to help you locate any potential source of threats faster.
- Build up confidence: Finally, encourage open communication between users and CIOs; and also raise awareness of the benefits of using controlled applications within the enterprise. Most importantly, do not hold back innovation. Whether employees develop applications or use tools in an unauthorized manner, these practices can be the perfect opportunity to find new ways to solve problems, increase workflow efficiency and improve business competitiveness through new tools. So look for a strategy that rather than prohibiting certain applications, allows you to support users in the use of innovative solutions.
The Risks of Shadow IT[6]
According to Cisco, 80% of end users use software not cleared by IT, 83% of IT staff admit to using unsanctioned software or services, and only 8% of all enterprises actually know the scope of shadow IT within their organization! Shadow IT, without a doubt, adds risk into your organization, and your employees are your weak link. Michael Bruemmer, vice president of Experian Data Breach Resolution explained, “As we have seen in our incident response service that we do for clients, about 80% of all the breaches we service have a root cause in some type of employee negligence.” When non-sanctioned applications and devices are in use, vulnerabilities can be introduced into the infrastructure, and without IT oversight, the root cause is very difficult to find. Some examples of the risk that shadow IT introduces includes:
- Software Asset Management (SAM): Organizations need to track all software applications used and licensing information. Unauthorized software makes this already difficult task nearly impossible, leading to our next risk.
- Compliance: Unauthorized applications once discovered can mandate a complete audit of the infrastructure to ensure you are compliant. Organizations that do not take this seriously risk hefty fines for non-compliance.
- Testing: IT infrastructures are complex organisms that require management. Introducing new applications without proper testing can compromise the entire infrastructure. Shadow IT also adds more complexity to the entire testing process by having to involve a third party.
- Configuration management: Creating a configuration management database (CMDB) and defining relationships between different systems is labor-intensive. When other employees use shadow IT, those systems are not included and can have compatibility issues as a result.
Criticism of Shadow IT[7]
Traditional enterprise IT departments place a premium on control and centralisation, and don’t like end users going behind their backs, especially when it implies that what IT provides is not good enough. The most common complaints are that it:
- Creates inconsistency in business logic and approach, as different parts of the organisation may end up using different IT services and processes that do not necessarily integrate.
- Adds extra cost to the business, as the business has to pay for its traditional services as well as shadow IT, and these generally are not under the same budget or subject to the same scrutiny in terms of costs/benefits.
- Creates inefficiencies, as the business needs to support more than one service, which can lead to duplicate support and system integration costs.
- Increases security risks, as data held in shadow IT services may not be managed, maintained and secured in the same way corporate data is.
- Constitutes a barrier to enhancing IT services, as end users, satisfied by shadow IT, may not feel the need to push for better services from the IT department.
Advantages of Shadow IT[8]
- It lets employees create their own solutions: Application development has long been a pain point in many businesses. In fact, it’s one reason why users turned to Shadow IT in the first place. They got tired of waiting on new applications from IT and decided to take matters into their own hands. They find tools that either meet their needs or let them build their own applications. When properly managed, the IT department can provide end users with the tools they need to create their own solutions. This lets IT control the data and user access, and lets users create the applications they need–without making requests to IT.
“Executives and IT departments increasingly view Shadow IT as an opportunity for employee innovation and cost management, rather than a significant security and control risk to the enterprise,” says James Quigley, CEO of Canvas. “This shift in thinking is in part due to an emerging set of applications that enable non-IT specialists throughout the organization to become “citizen developers” empowered to quickly and easily build and deploy solutions that address a specific pain point — without IT department support.”
- It delivers solutions closely aligned with business needs: Besides the problem of waiting around on solutions, another issue commonly occurs. When business users request solutions from IT, the details often get lost in translation. As a result, the finished product isn’t exactly what the user requested. Shadow IT helps address this problem, as it eliminates the risk of miscommunication. When the users are the ones finding/building their own solutions, they find solutions that better align with their goals.
“Shadow IT will generally yield a solution more closely aligned with the original business need with less emphasis on technology capabilities and more emphasis on the appropriateness, alignment, and the speed of delivery of the end product,” Dirk Garner, Principal Consultant at Garner Software. “Scheduling is simpler with Shadow IT delivered solutions as there is at least one fewer group participating in the project therefore there are fewer scheduling constraints.”
- It removes obstacles and improves productivity: Employees turn to Shadow IT when they can’t get the solutions they need, or to get around restrictions set up by the business. In many businesses, the IT department is viewed as an obstacle rather than a partner. Or, strict corporate policies make it hard to accomplish much of anything. When you embrace Shadow IT, you can give employees the tools they need for their everyday tasks. As a result, they spend less time looking for workarounds, and more time getting things done.
“Usually, I believe Shadow IT is a bad thing, but it does have a few benefits,” says Curtis Peterson, Digital Marketing Manager at SmartFile. “One, it shows initiative and ingenuity by your employees to overcome obstacles in their day. Your employees are more productive and efficient, and often will take ownership of the item. While your everyday employee might not foresee the security flaws and risks, they will become more efficient in their everyday work.”
- It Lessens the burden on the IT department: In most companies, the IT department is overworked. They keep the technology running, support the business, and are constantly putting out fires. Handling end-user requests for new solutions only add to their list of tasks. When Shadow IT is embraced, end users have access to a variety of pre-approved solutions, or the tools to create their own. This removes a burden from the IT department and lets them focus on other, mission-critical tasks.
“Most IT departments face a perpetually long list of IT project requests from employees and business units,” says Quigley. “Requests are arranged by their perceived significance to the organization financially, operationally or politically, and as a result, the project requests that tend to get the short end of the stick are internally facing applications, such as a solution to streamline logistics. Shadow IT empowers employees with these internally facing technology requests to see an application through from ideation to deployment, in turn allowing IT staff to focus on higher-level innovation projects that require deeper IT integration or more technically capable resources.”
See Also
- IT Organization (information technology organization)
- Information Technology (IT)
- IT Operations (Information Technology Operations)
- IT Operations Management (ITOM)
- IT Optimization
- Compliance
- Risk Management
- Enterprise Risk Management (ERM)
- Enterprise Resource Planning (ERP)
- Data Center
- Data Management
- Enterprise Integration
- IT Governance
References
- ↑ Defining Shadow IT -Wikipedia
- ↑ Shadow IT's Effect on IT Departments -Webopedia
- ↑ Stealth IT - The Flip Side of BYOD-Dameware
- ↑ Establishing Policies Around Shadow IT-BMC Blogs
- ↑ How to Successfully Manage the Shadow IT -GB Advisors
- ↑ The Risks of Shadow IT -OneNeck
- ↑ Traditional criticism of Shadow IT -ITProPortal
- ↑ Advantages of Embracing Shadow IT -MRC
